In the modern landscape of software development, no application exists in isolation. Every system relies on a complex web of external inputs, ranging from third-party APIs and open-source libraries to cloud services and legacy integrations. While these dependencies accelerate development, they introduce significant risks regarding security, licensing, stability, and technical debt. Without a clear map of these relationships, organizations operate blind to potential vulnerabilities and compliance gaps.
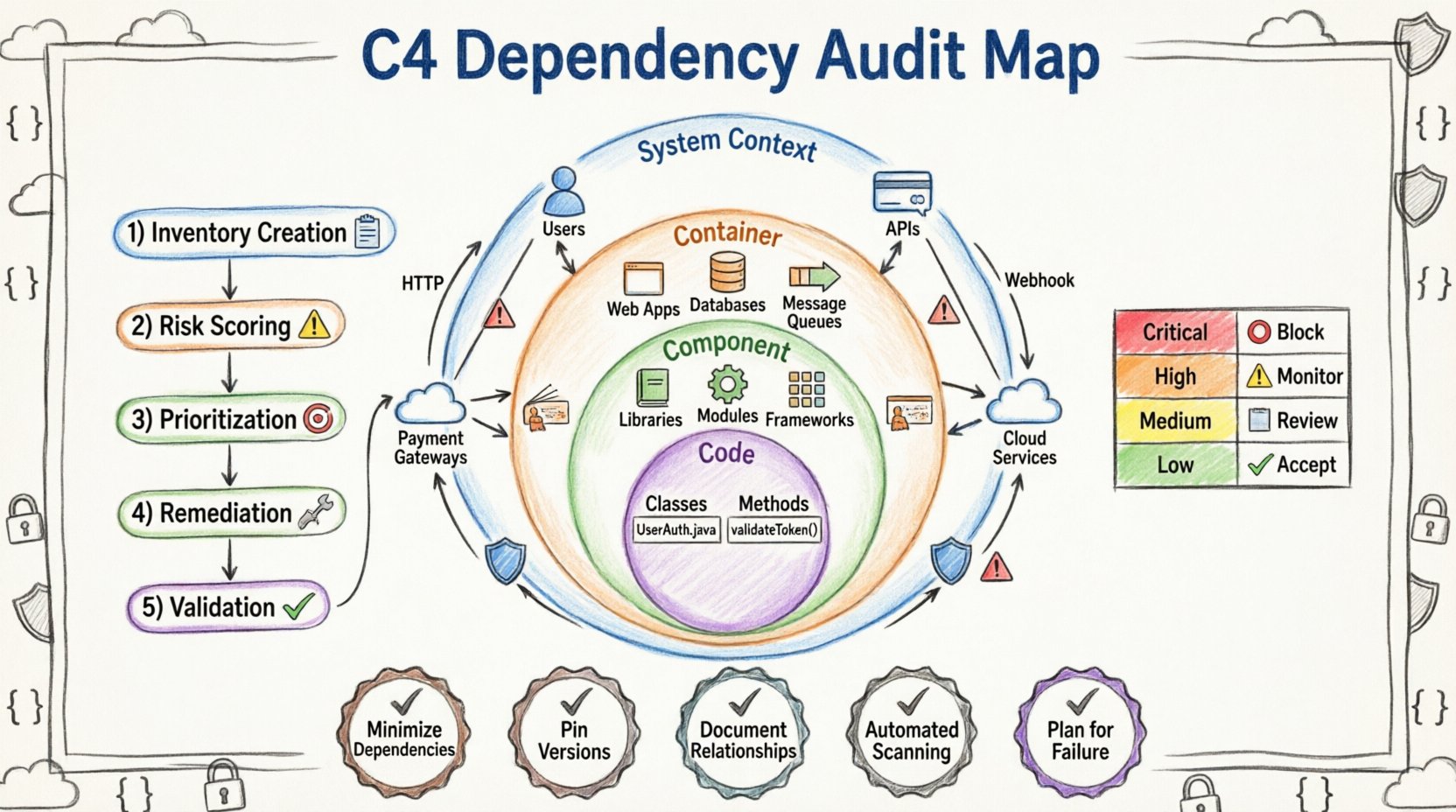
The C4 model provides a structured approach to visualizing software architecture. By leveraging Context, Container, Component, and Code levels, teams can systematically audit external dependencies. This guide details how to utilize C4 relationship maps to identify, assess, and manage the risks associated with external inputs.
🧩 Why Audit External Dependencies? 🛡️
Dependency management is often treated as a secondary concern until a critical vulnerability is discovered. However, proactive auditing ensures long-term system health. The primary motivations for auditing include:
- Security Posture: External libraries may contain known vulnerabilities (CVEs). Mapping them allows for targeted patching.
- Licensing Compliance: Open-source software carries licenses. Mixing incompatible licenses can lead to legal disputes.
- Vendor Risk: If a third-party API shuts down or changes its contract, your system breaks. Auditing reveals single points of failure.
- Technical Debt: Dependencies that are no longer maintained become liabilities. Identifying them early prevents future refactoring.
- Performance Impact: Heavy external calls can bottleneck internal systems. Visualizing these flows helps optimize latency.
🏗️ Understanding the C4 Model Hierarchy 📊
The C4 model organizes software architecture into four hierarchical levels. When auditing dependencies, each level reveals different types of external relationships. Understanding these distinctions is crucial for a comprehensive audit.
- System Context Diagram: This is the highest level. It shows the system being built and the people and other systems it interacts with. External dependencies here are typically third-party services, users, or external infrastructure.
- Container Diagram: This level breaks down the system into runtime instances (e.g., web apps, mobile apps, databases). Dependencies here are often protocols, APIs, or data stores.
- Component Diagram: This dives into the internal structure of a container. Dependencies here are libraries, frameworks, or modules.
- Code Diagram: This focuses on specific classes and methods. Dependencies here are rarely external in the traditional sense, but rather internal coupling.
For the purpose of auditing external dependencies, the System Context and Container levels are the most critical. They define the boundaries where external risk enters the system.
🌐 Mapping External Systems at the Context Level 🔗
The System Context diagram defines the perimeter. Auditing at this level answers the question: “Who or what is outside this boundary that touches this system?”
1. Identifying External Actors and Systems
Begin by listing all external entities interacting with the system. These might include:
- Customer-facing portals
- Internal enterprise systems
- Payment gateways
- Email service providers
- Authentication providers (SSO)
2. Analyzing Data Flows
For every connection arrow in the diagram, analyze the data traveling across it. This involves:
- Directionality: Is data sent, received, or both? Unidirectional flows might indicate batch processing or logging, which carries different risks than bidirectional transactions.
- Data Sensitivity: Does the external system receive Personally Identifiable Information (PII)? This impacts compliance requirements.
- Authentication: How does the external system verify the connection? API keys, OAuth tokens, or mutual TLS?
3. Assessing Dependency Criticality
Not all external systems are equal. Some are critical, while others are optional. A matrix helps categorize them:
| Category | Definition | Audit Priority |
|---|---|---|
| Critical | System cannot function without this dependency. | High |
| Important | Features degrade but core functions remain. | Medium |
| Optional | Enhances experience but is not required. | Low |
Critical dependencies require the most rigorous monitoring and contingency planning. If a critical external service goes down, the team must have a documented fallback strategy.
📦 Identifying Libraries and Services at the Container Level 🧱
The Container level represents the runtime environment. Here, dependencies are often technical interfaces. Auditing at this stage requires a deeper dive into the infrastructure.
1. Cataloging Runtime Dependencies
Every container relies on underlying infrastructure to run. This includes:
- Operating system images
- Middleware (e.g., web servers, message queues)
- Database engines
- Container orchestration platforms
These components often receive security patches from external vendors. Auditing involves verifying that the versions in use are supported and free of known vulnerabilities.
2. API and Protocol Audits
Containers communicate via APIs. These are prime targets for dependency risk. When reviewing API interactions:
- Versioning: Is the API version still supported? End-of-life APIs must be migrated.
- Rate Limiting: Does the external provider limit requests? Sudden spikes could cause throttling.
- Endpoints: Are all endpoints necessary? Unused endpoints increase the attack surface.
3. Infrastructure as Code (IaC)
Modern systems define infrastructure in code. This code itself contains dependencies on configuration repositories or template libraries. Auditing IaC ensures that the blueprint for the system is secure and up-to-date before deployment.
🔧 Component-Level Dependency Analysis 🧩
While Context and Container levels deal with macros, the Component level deals with the software logic itself. This is where the majority of open-source libraries reside.
1. The Transitive Dependency Problem
A component might depend on Library A. Library A depends on Library B. This is a transitive dependency. These hidden chains are often where vulnerabilities hide.
- Visibility: Ensure the build process generates a full dependency tree.
- Extraction: Identify all libraries, direct and transitive.
- Removal: If a transitive library is unused, remove the parent dependency that pulls it in.
2. License Verification
Each component carries a license. Mixing permissive licenses (like MIT) with copyleft licenses (like GPL) can create legal liabilities. An audit checklist should include:
- Verify the license of every component.
- Check for conflicts between components.
- Ensure the organization’s legal policy allows the usage of each license type.
3. Supply Chain Integrity
Ensure that the software came from a trusted source. Auditing involves verifying the provenance of the components. This includes checking digital signatures and ensuring the package registry has not been compromised.
🔄 The Audit Workflow: Step-by-Step ⚙️
Conducting a dependency audit is a process, not a one-time event. The following workflow ensures consistency and thoroughness.
Step 1: Inventory Creation
Generate a complete list of all dependencies. This should be an automated process where possible. Export the data into a central repository. Include metadata such as version, license, and last update date.
Step 2: Risk Scoring
Assign a risk score to each dependency based on:
- Vulnerability Status: Are there known CVEs?
- Maintenance Status: Is the project actively maintained?
- Adoption Rate: How many other organizations use this? High adoption often implies better security.
- Complexity: Does the dependency introduce significant complexity to the codebase?
Step 3: Prioritization
Not all risks can be fixed immediately. Prioritize based on the risk score and the criticality of the component. Focus resources on critical systems with high-risk dependencies first.
Step 4: Remediation
Execute the fixes. This may involve upgrading versions, replacing libraries, or refactoring code to remove the dependency entirely. Document every change made.
Step 5: Validation
After remediation, verify that the system still functions correctly. Run automated tests to ensure no regressions were introduced by the dependency changes.
🛠️ Risk Assessment Matrix 📉
To facilitate decision-making, use a standardized matrix to categorize the severity of dependency issues. This helps stakeholders understand the urgency.
| Risk Level | Criteria | Action Required |
|---|---|---|
| Critical | Active exploit, critical data exposure, or system crash. | Immediate patch or replacement required. |
| High | Known vulnerability, unsupported version, or license conflict. | Fix within the next sprint or release cycle. |
| Medium | Deprecated features, minor security advisories. | Monitor and schedule for future update. |
| Low | Minor documentation issues, cosmetic bugs. | Address during regular maintenance. |
🔄 Maintenance and Continuous Monitoring 🔄
An audit is not a destination; it is a checkpoint. Dependencies evolve. New vulnerabilities are discovered daily. Continuous monitoring ensures the system remains secure over time.
1. Automated Scanning
Integrate scanning tools into the build pipeline. Every time code is committed, the system should check the dependency tree against a vulnerability database. This prevents new risks from being introduced.
2. Scheduled Reviews
Even with automation, schedule quarterly reviews of the dependency map. This allows human analysis of the architecture to catch issues that scanners might miss, such as business logic risks or vendor lock-in.
3. Change Management
Require approval for any dependency update in production. Small version bumps can have large impacts. The audit map should be updated whenever a dependency is added, removed, or modified.
🚫 Common Pitfalls in Dependency Audits 🙅
Auditing is prone to human error. Being aware of common mistakes helps avoid them.
- Ignoring Transitive Dependencies: Focusing only on direct dependencies leaves the system exposed to vulnerabilities hidden deep in the library tree.
- Static Maps Only: Creating a map once and never updating it renders it useless. The map must be a living document.
- Lack of Context: Knowing a library has a vulnerability is not enough. Knowing if that library is actually used in a critical path determines the real risk.
- Over-Reliance on Automation: Tools are powerful, but they cannot understand business logic. Human review is essential for architectural decisions.
- Ignoring Licensing: Security is not the only risk. Legal risks from licensing can shut down a product just as effectively as a bug.
✅ Best Practices for Sustainable Auditing ✅
To build a resilient system, adopt these best practices into the development culture.
- Minimize Dependencies: Every dependency is a risk. Prefer standard libraries over third-party packages when possible.
- Pin Versions: Always specify exact versions in configuration files to prevent automatic updates to unstable versions.
- Document Relationships: Keep the C4 diagrams up to date. If a dependency changes, update the map.
- Engage Security Teams: Make the audit a collaborative effort between developers, architects, and security specialists.
- Plan for Failure: Assume dependencies will fail. Build circuit breakers and fallback mechanisms into the architecture.
🏁 Final Thoughts on Architecture Visibility 🎯
External dependencies are inevitable in software engineering. The goal is not to eliminate them, but to understand them. By using the C4 model to visualize these relationships, teams gain visibility into the hidden costs of their architecture.
This approach shifts dependency management from a reactive task to a proactive strategy. It empowers teams to make informed decisions about which tools to use, how to secure them, and when to retire them. In a world of increasing complexity, a clear map is the most valuable asset a team can possess.
Start mapping your dependencies today. Use the C4 levels to structure your audit. Ensure that every external connection is accounted for, assessed, and monitored. This discipline forms the foundation of a secure and maintainable software ecosystem.