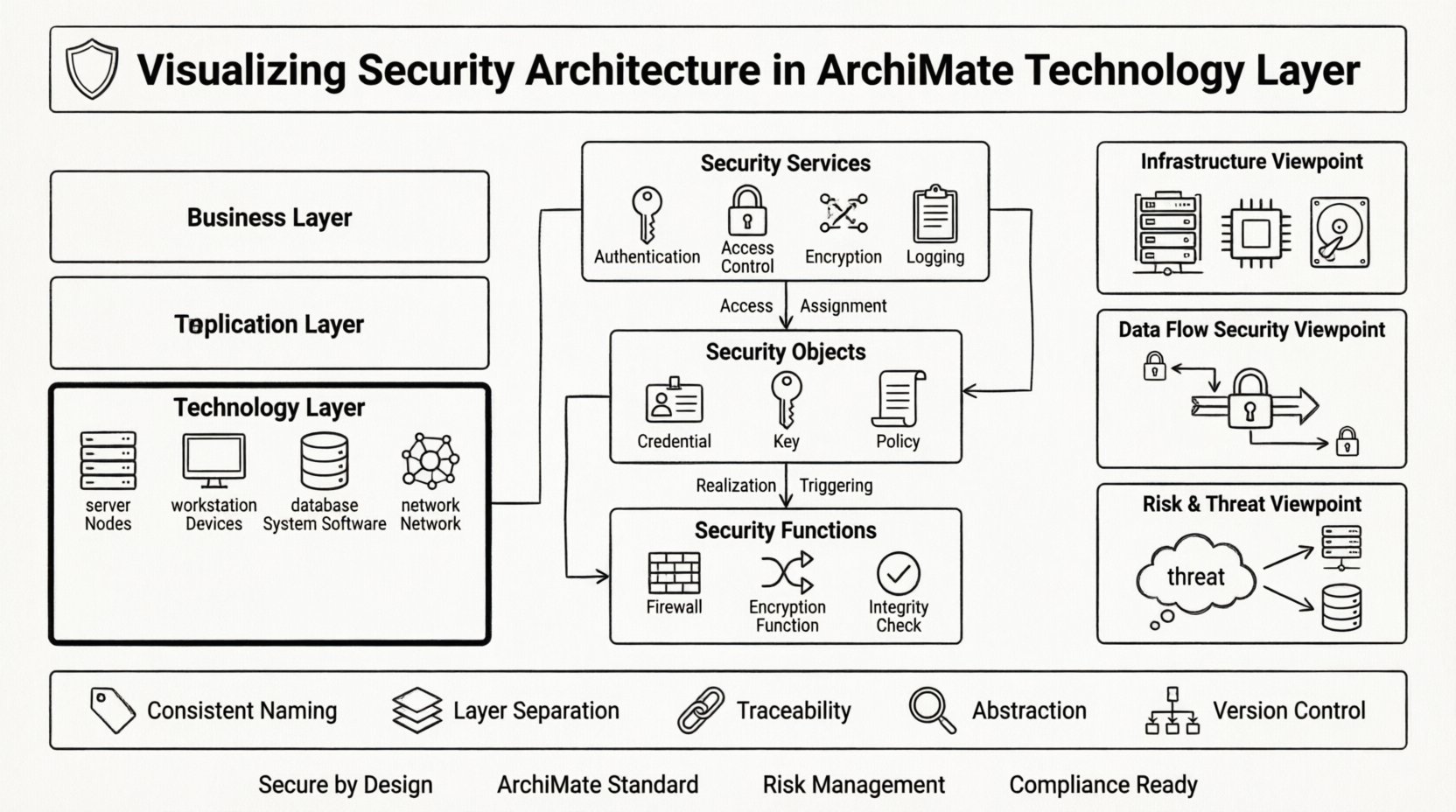
Enterprise architecture demands precision when addressing the backbone of information systems. The Technology Layer serves as the hardware and software infrastructure that supports applications and business processes. Within this layer, security is not an afterthought but a foundational element that requires explicit modeling. Visualizing security architecture in ArchiMate ensures that protection mechanisms are visible, traceable, and integrated into the broader system design. This guide explores the specifics of representing security controls, services, and threats within the Technology Layer using the ArchiMate standard.
Security modeling often becomes fragmented when teams rely on ad-hoc diagrams or text-based specifications. A standardized approach allows stakeholders to understand how security policies translate into technical implementations. By using the ArchiMate framework, architects can map the flow of data, the placement of cryptographic functions, and the enforcement of access rights across devices and systems. This visibility supports risk assessment, compliance reporting, and change management without relying on proprietary tools or external software products.
Understanding the Technology Layer 🖥️
The Technology Layer sits at the bottom of the ArchiMate three-layer stack. It represents the physical and virtual resources that support the execution of applications. When visualizing security here, the focus shifts from logical business rules to physical and logical constraints. This layer includes nodes, devices, system software, and networks. Each element can host security functions or be subject to security policies.
- Nodes: Represent physical or logical computational resources.
- Devices: Specific hardware components like servers, workstations, or sensors.
- System Software: Operating systems, databases, and middleware that manage resources.
- Network: Communication infrastructure connecting nodes and devices.
Security in this context involves protecting the integrity, availability, and confidentiality of these resources. It is not enough to state that a server is “secure.” The model must define how it is secured. This includes encryption methods, physical access controls, and network segmentation strategies.
Core Security Elements in ArchiMate 🛡️
To model security effectively, one must utilize specific metamodel elements designed for security concerns. ArchiMate provides a dedicated subset of elements for security, primarily within the Application and Technology layers. These elements allow for the distinction between security services, security objects, and security functions.
Security Services
Security services represent capabilities provided by the infrastructure to protect data and resources. In the Technology Layer, these services are often implemented through system software or dedicated hardware modules.
- Authentication Service: Verifies the identity of users or systems accessing the technology.
- Access Control Service: Manages permissions and authorization policies.
- Encryption Service: Provides cryptographic functions for data at rest and data in transit.
- Logging Service: Records security-related events for auditing and monitoring.
Security Objects
Security objects are artifacts or resources that hold security information or serve as the target of security measures. In the Technology Layer, these often manifest as data stored on devices or keys held within system software.
- Security Credential: Passwords, tokens, or certificates used for authentication.
- Security Key: Cryptographic keys used for encryption or signing.
- Security Policy: Rules that define security requirements and constraints.
Security Functions
Security functions are specific actions or processes that enforce security. They are often realized within system software or specialized security devices.
- Firewall Function: Filters network traffic based on rules.
- Encryption Function: Transforms data to prevent unauthorized access.
- Integrity Check: Verifies that data has not been altered.
Relationships & Dependencies 🔗
Modeling security is not just about placing elements; it is about defining the relationships that connect them. Relationships show how security services protect objects, how functions realize services, and how threats interact with assets. The following table outlines key relationships relevant to the Technology Layer.
| Relationship Type | Source | Target | Description |
|---|---|---|---|
| Access | Security Service | Security Object | Describes which service protects or accesses which object. |
| Assignment | Security Function | Security Service | Links a specific function to the service it enables. |
| Realization | Security Object | Security Service | Indicates that an object implements or supports a service. |
| Triggering | Threat | Security Function | Shows that a threat activates a specific security response. |
Understanding these connections is vital for impact analysis. If a specific encryption service is removed, the model reveals which security objects are exposed. If a network device is compromised, the relationships show which data flows are at risk. This granularity supports proactive risk management rather than reactive patching.
Security Viewpoints 👁️
A viewpoint defines the perspective from which a model is viewed. It determines which elements and relationships are included to address specific stakeholder concerns. In the Technology Layer, security architects require specific viewpoints to communicate effectively with infrastructure teams and auditors.
Security Infrastructure Viewpoint
This viewpoint focuses on the physical and logical components that enforce security. It highlights devices, system software, and network segments.
- Stakeholders: Infrastructure managers, hardware architects.
- Focus: Placement of firewalls, encryption modules, and access control points.
- Key Elements: Nodes, devices, system software, security services.
Data Flow Security Viewpoint
This viewpoint tracks how data moves through the technology layer and where protections are applied. It is essential for understanding data lineage and exposure points.
- Stakeholders: Data protection officers, compliance teams.
- Focus: Encryption points, data storage locations, transmission paths.
- Key Elements: Data objects, communication flows, encryption services.
Risk & Threat Viewpoint
This viewpoint maps threats against technology assets and their corresponding security functions. It aids in risk assessment and mitigation planning.
- Stakeholders: Risk managers, security analysts.
- Focus: Vulnerabilities, threats, security controls, residual risk.
- Key Elements: Threats, security functions, security objects.
Modeling Best Practices ✅
Creating a robust security model requires discipline and adherence to established patterns. The following practices help maintain clarity and utility in the architecture.
- Consistent Naming: Use clear, descriptive names for security services and objects. Avoid generic terms like “Security1”.
- Layer Separation: Keep security concerns distinct from business logic. While they interact, the Technology Layer should focus on technical enforcement.
- Traceability: Ensure every security requirement traces back to a business goal or regulatory mandate. This linkage justifies the investment in specific security measures.
- Abstraction Levels: Do not model every single firewall rule. Use abstraction to show high-level security zones and trust boundaries.
- Version Control: Security architectures change frequently. Maintain versions of the model to track how security posture evolves over time.
Integration with Business & Application Layers 🔄
Security cannot exist in isolation. The Technology Layer interacts with the Application and Business Layers. Understanding these interactions is critical for a holistic view of enterprise security.
Technology to Application
Applications rely on technology services to function securely. An application may require an authentication service provided by the technology layer. The model should show which applications consume which security services.
- Usage Relationship: Application elements use technology security services.
- Access Control: Applications enforce business rules, but technology enforces system access.
Technology to Business
Business processes have security requirements that must be met by the underlying technology. For example, a financial transaction process may require end-to-end encryption. The model must link the business process to the technology service that fulfills the requirement.
- Assignment: Business process assignments to technology security functions.
- Compliance: Mapping regulatory requirements to specific technology controls.
Common Challenges & Solutions ⚠️
Modeling security in the Technology Layer presents specific difficulties. Recognizing these challenges helps architects navigate the complexity of enterprise environments.
Challenge 1: Complexity Overload
Issue: Including every security device and rule results in an unreadable diagram.
Solution: Use multiple viewpoints. Create a high-level overview for leadership and detailed sub-models for technical teams. Leverage grouping to aggregate similar devices into security zones.
Challenge 2: Dynamic Environments
Issue: Cloud and virtual environments change rapidly, making static models obsolete quickly.
Solution: Focus on logical relationships rather than physical locations. Model the function of security rather than the specific server instance. Use tags or attributes to denote dynamic properties like “Cloud-Hosted”.
Challenge 3: Lack of Standardization
Issue: Different teams use different terminology for the same security concepts.
Solution: Establish a glossary of terms within the architecture repository. Ensure all security services follow the ArchiMate metamodel definitions to maintain consistency across the enterprise.
Challenge 4: Visibility of Threats
Issue: Threats are often external and hard to model within the internal architecture.
Solution: Introduce threat actors and threat events as external elements. Connect them to the technology layer to show potential impact points. This visualizes the attack surface clearly.
Step-by-Step Modeling Approach 📝
Implementing a security model follows a logical progression. This approach ensures that all necessary elements are captured without skipping critical details.
- Identify Assets: Determine the critical data and devices within the Technology Layer that require protection.
- Define Services: List the security services needed to protect these assets (e.g., authentication, encryption).
- Map Functions: Specify which system software or hardware functions will deliver these services.
- Establish Relationships: Connect services to objects and functions to services using the appropriate ArchiMate relationships.
- Validate with Viewpoints: Review the model through different stakeholder viewpoints to ensure clarity and completeness.
- Document Assumptions: Record any assumptions made about the environment, such as trust levels between network segments.
Ensuring Compliance & Auditability 🔍
One of the primary benefits of visualizing security architecture is the ability to demonstrate compliance. Regulators and auditors often require evidence that security controls are in place and functioning.
- Mapping Controls: Link specific ArchiMate security objects to compliance standards (e.g., ISO 27001, NIST).
- Traceability Reports: Generate reports that show the lineage from a business requirement to a technology control.
- Gap Analysis: Use the model to identify missing controls. If a business process requires encryption, the model should show the encryption service. If it is missing, a gap is identified.
This structured approach transforms security from a black box into a visible, manageable component of the enterprise architecture. It enables architects to make informed decisions about resource allocation and risk tolerance.
The Role of Data in Security 📊
Data is often the primary asset being protected. In the Technology Layer, data objects reside on devices or within system software. The security model must explicitly show where sensitive data is stored and how it is protected.
- Data Classification: Tag data objects with sensitivity levels (e.g., Public, Confidential, Restricted).
- Storage Security: Indicate if data is encrypted at rest. Model the encryption service associated with the storage device.
- Transmission Security: Show how data moves between nodes. Model the network security services applied to these paths.
By integrating data classification into the model, architects can prioritize protection efforts. High-value data receives stronger security controls, while lower-value data may have lighter restrictions. This aligns security spending with business value.
Conclusion on Visualization 🔚
Visualizing security architecture in the ArchiMate Technology Layer provides a structured method for understanding and managing risk. It bridges the gap between high-level business requirements and low-level technical implementation. By using standardized elements, relationships, and viewpoints, architects can create models that are both technically accurate and communicatively effective.
The process requires attention to detail and a commitment to maintaining the model as the environment evolves. However, the payoff is a clear understanding of where security controls exist, where they are missing, and how they interact with the rest of the enterprise. This clarity is essential for building resilient systems that can withstand modern threats while supporting business objectives.
Adopting these practices ensures that security architecture is not just a theoretical exercise but a practical tool for decision-making. It empowers teams to design systems that are secure by design, rather than secure by accident. Through disciplined modeling, the Technology Layer becomes a foundation of trust within the enterprise.