Designing a robust database schema for a multitenant environment requires a fundamental shift in thinking compared to single-tenant architectures. When multiple customers, or tenants, share the same underlying infrastructure, the Entity Relationship Diagram (ERD) becomes the blueprint for data segregation, security, and performance. 🏗️ A poorly constructed ERD can lead to data leaks, performance degradation, and complex migration paths. This guide explores the structural intricacies of modeling multitenant systems without relying on specific software tools, focusing instead on architectural principles.
Understanding the Core Challenge of Shared Data 🏢
In a traditional single-tenant setup, every customer has their own isolated database. The relationship between the application and the data is one-to-one. However, in a multitenant system, the relationship is one-to-many. The application serves multiple tenants from a shared pool of resources. The ERD must explicitly encode the context of the tenant into every query and transaction.
The primary goal is to ensure that Tenant A never sees data belonging to Tenant B, even if they query the exact same table. This is often referred to as logical isolation. The ERD must support this isolation natively through schema design, rather than relying solely on application logic. 🔒
Isolation Models and Their Impact on Schema Design 🏗️
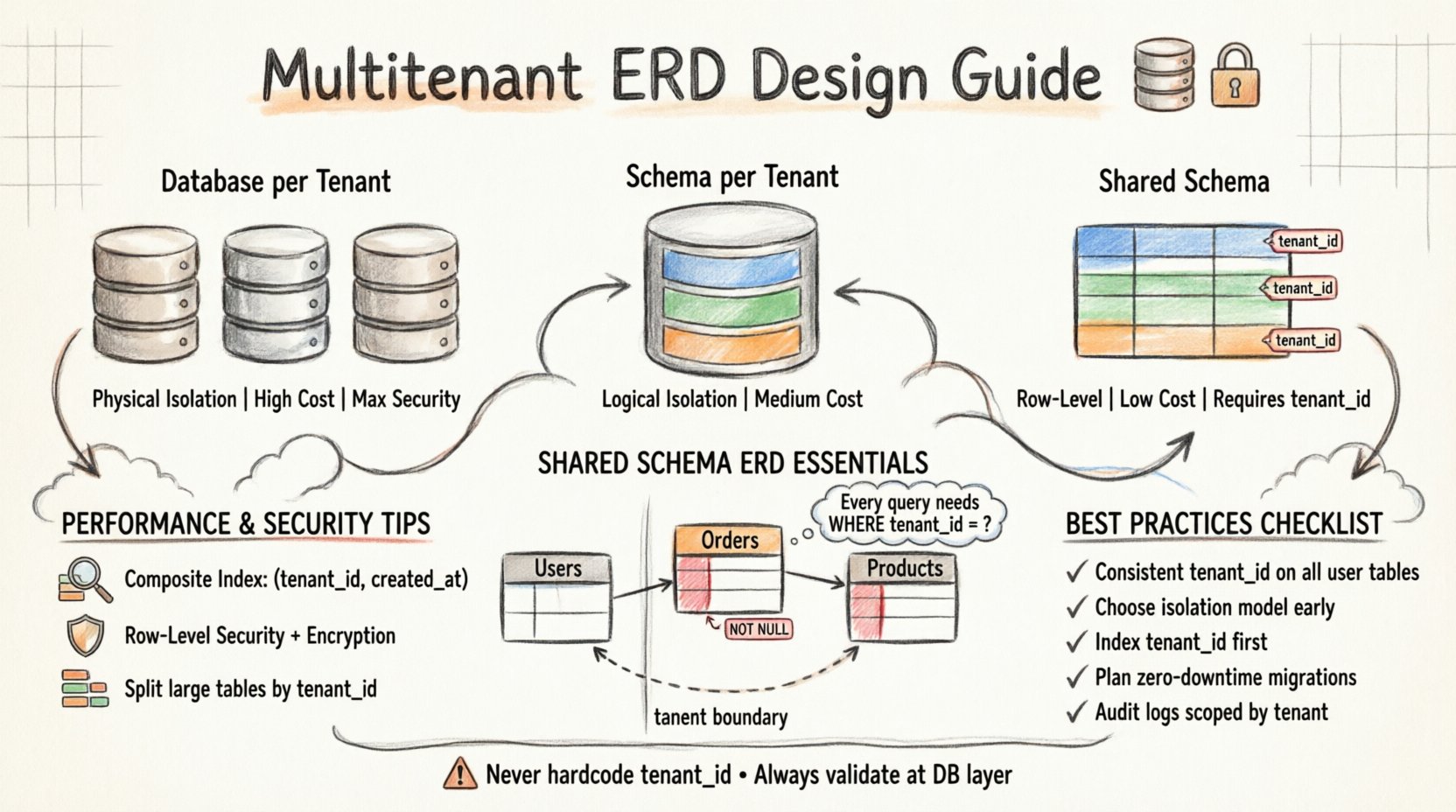
There are three primary models for isolating tenant data. Each model dictates a significantly different approach to the Entity Relationship Diagram. Choosing the wrong model early in the design phase can force a costly rewrite later.
1. Database per Tenant (Physical Isolation)
In this model, each tenant gets their own physical database instance. The ERD remains identical to a single-tenant design. Every table exists independently in its own database container.
- Pros: Maximum security and isolation. Data leaks are physically impossible between tenants.
- Cons: High operational cost. Managing hundreds or thousands of databases is complex.
- Schema Implication: The ERD does not need to account for a tenant identifier column because the database itself acts as the identifier.
2. Schema per Tenant (Logical Isolation)
Multiple tenants share a single database, but each tenant has their own schema (namespace) within that database. The ERD remains largely the same as the single-tenant version, but the schema name changes based on the tenant.
- Pros: Better isolation than shared tables. Easier to manage than individual databases.
- Cons: Query complexity increases as the application must switch schemas dynamically.
- Schema Implication: The ERD does not require a tenant ID column in every table. Instead, the database connection context handles the separation.
3. Shared Schema, Shared Tables (Logical Isolation)
This is the most common model for SaaS applications. All tenants share the exact same tables. The ERD must be modified to include a unique identifier for each tenant in every relevant row.
- Pros: Lowest cost and operational overhead. Easier to run global analytics.
- Cons: Highest risk of data leakage if logic fails. Performance can suffer as tables grow large.
- Schema Implication: Every table must include a
tenant_idcolumn. Foreign keys must reference this column to maintain integrity.
Designing the Shared Schema ERD 🔑
When adopting the Shared Schema model, the ERD requires specific modifications to ensure data integrity and security. This section details the critical components that must appear in your diagrams.
The Tenant Identifier Column
Every table that holds user-specific data must include a column to identify the owner of that data. This column is typically named tenant_id or organization_id.
- Data Type: Should be an integer or a UUID. Integers are generally faster for joins.
- Not Null Constraint: This column should never be nullable. A null value implies the data belongs to no one, which violates the multitenant contract.
- Default Value: In some applications, the default might be set at the application level, but the database schema should enforce the presence of this value.
Foreign Key Relationships
When tables relate to one another, the relationship must respect tenant boundaries. A common mistake is creating a relationship between a global table (like a Product Catalog) and a tenant-specific table (like an Order).
- Global Tables: Tables like
ProductsorCategoriesmight be shared. They do not need atenant_id. - Tenant Tables: Tables like
OrdersorUsersmust have atenant_id. - Join Logic: When joining a global table to a tenant table, the join condition must include the
tenant_idmatch to prevent cross-tenant data exposure.
Comparing Isolation Strategies 📊
Understanding the trade-offs is essential for selecting the right ERD structure. The following table outlines the key differences between the primary isolation strategies.
| Strategy | Isolation Level | Cost | Management Complexity | Schema Requirement |
|---|---|---|---|---|
| Database per Tenant | Physical | High | High | Standard (No Tenant ID) |
| Schema per Tenant | Logical | Medium | Medium | Standard (Schema Name) |
| Shared Schema | Row-Level | Low | Low | Requires Tenant ID Column |
Performance Considerations in ERD Design 🚀
As data accumulates, the performance of a shared schema can degrade. The ERD must support indexing strategies that optimize for tenant-specific queries.
Indexing Strategies
Without proper indexing, a query to fetch data for one tenant might scan the entire table, which includes millions of rows from other tenants.
- Composite Indexes: Create indexes that start with the
tenant_id. For example, an index on (tenant_id,created_at) allows the database to quickly locate the specific tenant’s records and sort them. - Covering Indexes: If you frequently query specific columns, include them in the index to avoid table lookups.
- Partitioning: Large tables can be partitioned by
tenant_id. This physically separates the data on disk, improving query speed and backup management.
Query Optimization
The application layer must ensure that every query includes the tenant_id in the WHERE clause. The ERD design should not rely on the application to filter data; the database should be the source of truth.
- Row-Level Security: Some database systems support Row-Level Security (RLS). The ERD can leverage this feature to automatically filter rows based on the authenticated user’s context.
- Query Plans: Regularly review query execution plans. Ensure the database is using the
tenant_idindex and not performing a full table scan.
Security and Compliance Implications 🛡️
Data privacy regulations, such as GDPR and CCPA, impose strict requirements on how data is stored and accessed. The ERD plays a vital role in compliance.
Data Segregation
Compliance often requires that data be easily separable. If a tenant requests deletion of their data, the system must be able to locate and remove all records associated with their tenant_id.
- Soft Deletes: Instead of hard deleting rows, mark them as deleted. This is often safer for auditing. The
deleted_atcolumn should also be scoped bytenant_id. - Encryption: Sensitive fields within the tenant scope should be encrypted. The key management strategy must align with the tenant isolation model.
Auditing and Logging
Audit trails are essential for security. Every action taken on tenant data should be logged.
- Audit Table: Create a dedicated table for logs that includes the
tenant_idof the affected entity. - Access Control: Ensure that the audit log itself is protected. Administrators should not be able to see audit logs from tenants they do not manage.
Schema Evolution and Migration 🔄
Applications evolve. Features are added, and data structures change. In a multitenant environment, schema migrations are more complex because you must apply changes to all tenants without causing downtime or data loss.
Backward Compatibility
When modifying the ERD, ensure backward compatibility is maintained.
- Additive Changes: Adding a new column to a table is usually safe if it allows nulls.
- Removal of Columns: This is risky. A column should only be removed after ensuring no tenant is using it, and a deprecation period is established.
- Renaming Columns: This can break queries. It is better to add a new column, migrate data, and then switch references rather than renaming.
Zero-Downtime Migrations
For large tenants, locking tables during a migration is not an option. The ERD design should support online schema changes.
- Ghost Tables: Create a new table with the updated structure, copy the data, and then swap the tables.
- Versioning: Some systems support multiple versions of a schema simultaneously to allow for gradual rollout.
Common Pitfalls to Avoid ⚠️
Designing a multitenant ERD involves many moving parts. Here are common mistakes that compromise the system.
- Ignoring the Tenant ID: Forgetting to add the
tenant_idto a new table created during development. This leads to immediate data leakage risks. - Hardcoding IDs: Never hardcode a tenant ID in the application code. It must be passed dynamically at runtime.
- Global Counters: Avoid using global auto-increment counters if they are exposed in the URL or API responses, as this can reveal the number of tenants or users.
- Shared Files: The ERD focuses on the database, but file storage is often overlooked. Ensure file paths include the tenant identifier to prevent access issues.
Advanced Patterns for Complex Scenarios 🔍
Not all multitenant systems are created equal. Some require more granular control over the data structure.
Multi-Organization Support
One tenant might belong to multiple organizations, or vice versa. The ERD must support many-to-many relationships.
- Join Tables: Use a junction table to link users, tenants, and organizations.
- Permission Models: The ERD should support role-based access control (RBAC) at the tenant level.
Global vs. Tenant-Specific Settings
Some configuration data is global (app-wide), while other data is specific to a tenant.
- Settings Table: Structure the ERD to distinguish between global configuration and tenant-specific overrides.
- Inheritance: A tenant setting might inherit from a global default. The schema should reflect this hierarchy clearly.
Summary of Best Practices ✅
Building a secure and scalable multitenant system relies heavily on the foundation laid by the Entity Relationship Diagram. By adhering to the following principles, you can ensure long-term stability.
- Consistency: Ensure every table that holds user data includes the tenant identifier.
- Isolation: Choose an isolation model that matches your security and cost requirements.
- Performance: Design indexes that prioritize the tenant identifier.
- Security: Implement row-level security and encryption where appropriate.
- Maintainability: Plan for schema changes that do not disrupt service.
The design of your database schema is a strategic decision that affects the entire lifecycle of the application. A well-structured ERD prevents data leaks, ensures compliance, and supports growth. By carefully considering the nuances of multitenancy during the design phase, you create a foundation that is resilient and secure. 🏛️
Continuous review of the ERD as the application grows is necessary. New features often introduce new data relationships that must be evaluated against tenant isolation rules. Stay vigilant, document your design decisions, and prioritize data integrity above all else. This approach ensures that your architecture remains robust as you scale.